What’s træfik?
Træfik is a modern HTTP reverse proxy and load balancer. One could ask a question: “Why another rev-proxy since we already have nginx and ha-proxy available, mature and well tested around the world?”
While using ‘regular’ rev-proxy software like nginx you need to prepare configuration file for new vhost/service and reload the http frontend, so the new configuration can be applied. Let’s skip Jason’s nginx docker image, shall we?
Træfik has been designed to be used in front of microservices environment. It supports few popular backends (Docker, Swarm, Consul, Etcd and even Amazon ECS) to automatically configure the environment. As a new service, or container, is added or removed, the load balancer will reshape the traffic to match.
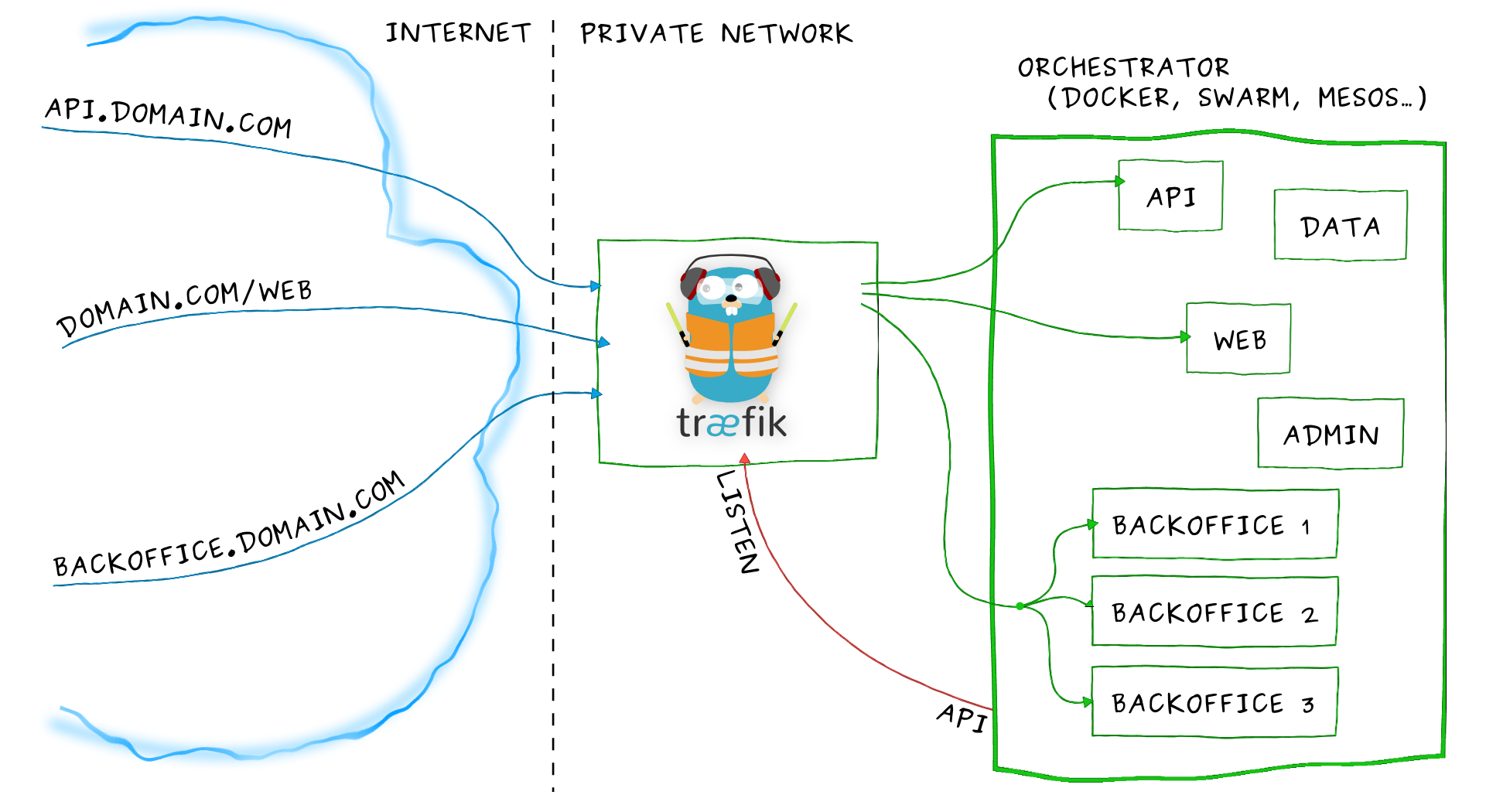 Image source: https://traefik.io/
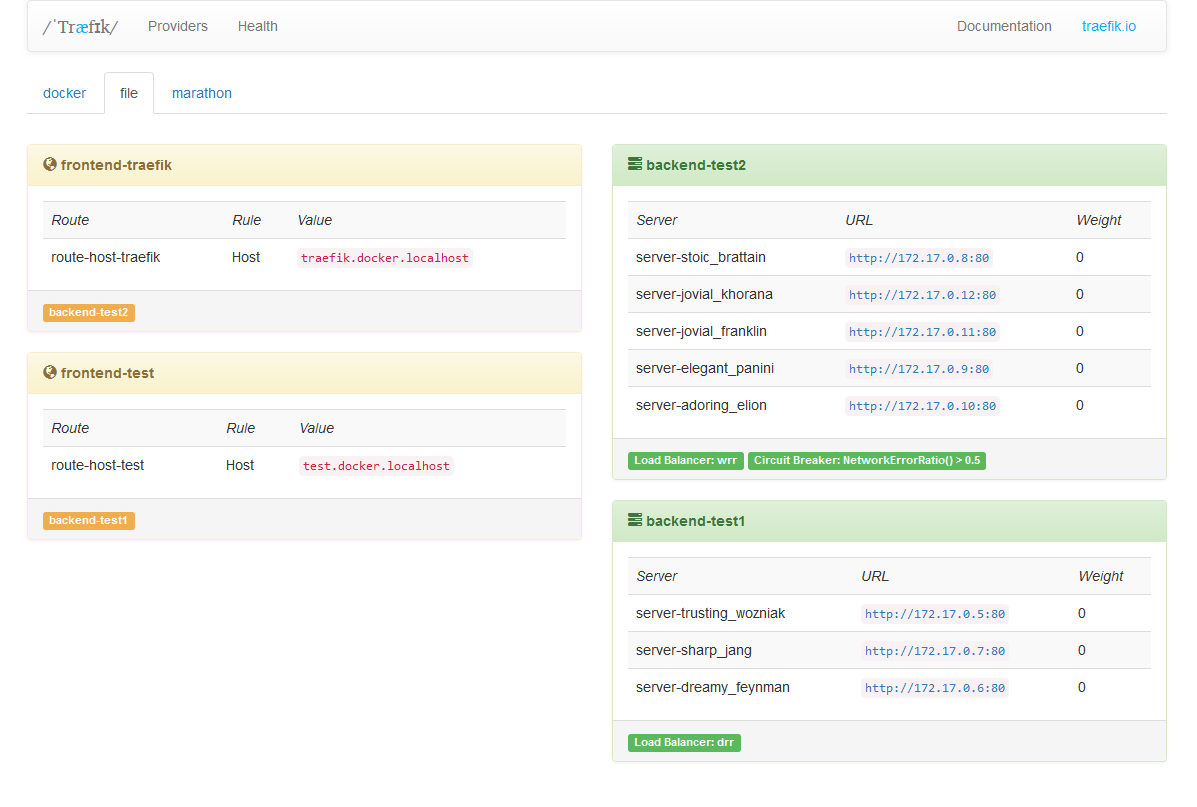
Image source: https://traefik.io/
Other features of træfik:
- Single binary thanks to go, no dependencies
- Rest API
- Hot-reloading of configuration
- HTTP2, websockets, proxy protocol ready!
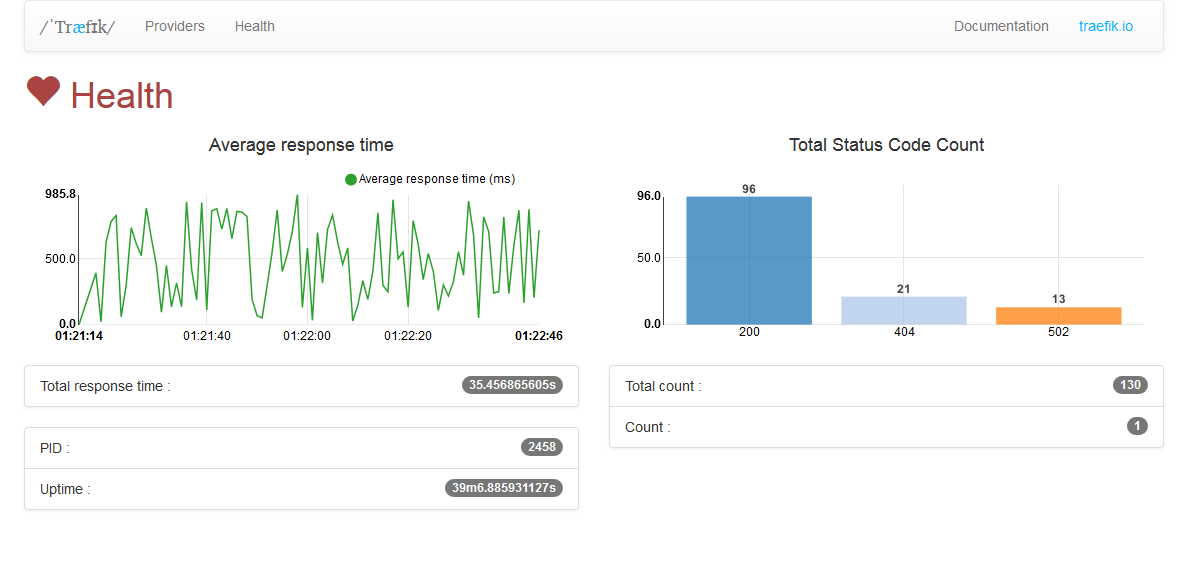
- Metrics
- AngularJS Web UI
- Let’s Encrypt support with automatic renewal
- few load balancing policies
Clean UI
Træfik has a simple Web UI based on AngularJS.
Demo
Surprise - Træfik can be run as a docker container.
But first we need to create configuration file.
$ vim traefik.toml
Add entry points http, https, that all backends will have access by default. Those entry points will be configured later.
defaultEntryPoints = ["http", "https"]
Configure web provider - this will give you access to web UI of træfik. This dashboard will run on 8080 port.
...
[web]
address = ":8080"
entryPoints section configures the addresses that træfik and proxied containers can listen on. We love 302 redirect to https, right?
...
[entryPoints]
[entryPoints.http]
address = ":80"
[entryPoints.http.redirect]
entryPoint = "https"
[entryPoints.https]
address = ":443"
[entryPoints.https.tls]
Add Let’s Encrypt to the setup.
...
[acme]
email = "email@domain.tld"
storage = "acme.json"
entryPoint = "https"
Save it. Configuration file ready.
Last steps. Create docker network docker network create proxy and create empty file for storing Let’s Encrypt data touch acme.json; chmod 600 acme.json
Start træfik.
$ docker run -d \ # as deamon
-v /var/run/docker.sock:/var/run/docker.sock \ # give access to docker socket
-v $PWD/traefik.toml:/traefik.toml \ # give access to configuration f ile
-v $PWD/acme.json:/acme.json \ # give access to let's encrypt storage
-p 80:80 \ # bind ports
-p 443:443 \
-l traefik.frontend.rule=Host:traefik.domain.tld \
-l traefik.port=8080 \
--network proxy \
--name traefik \
traefik --docker
For your peace of mind check the logs: docker logs traefik.
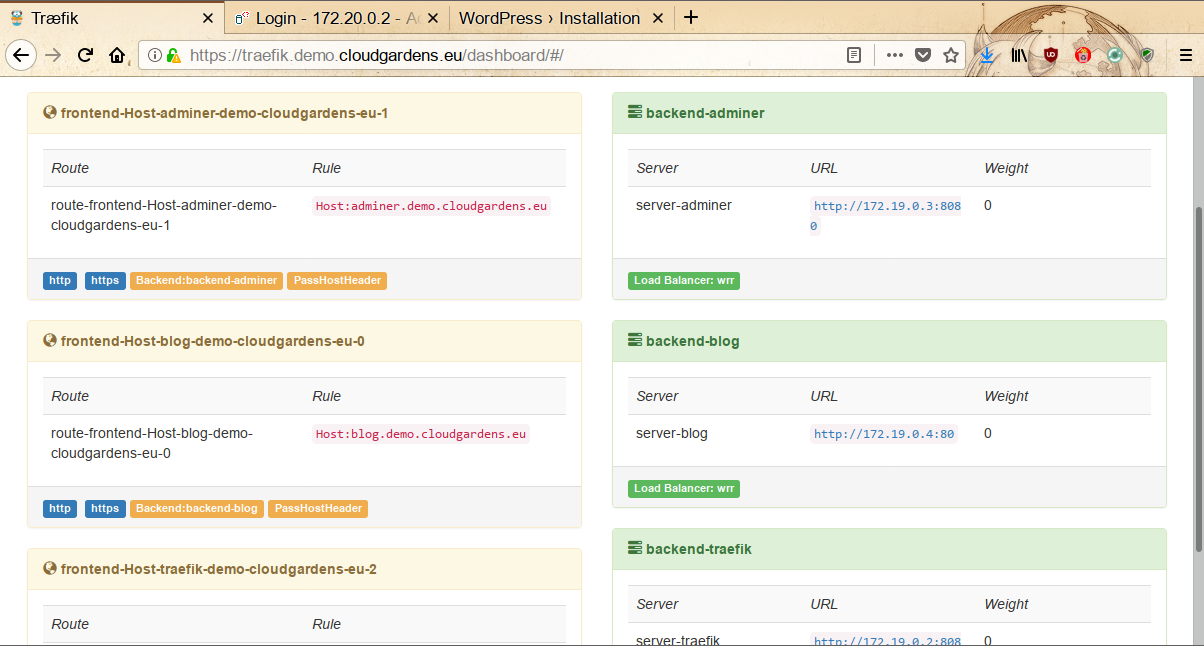
Go to https://traefik.domain.tld, dashboard should be there.
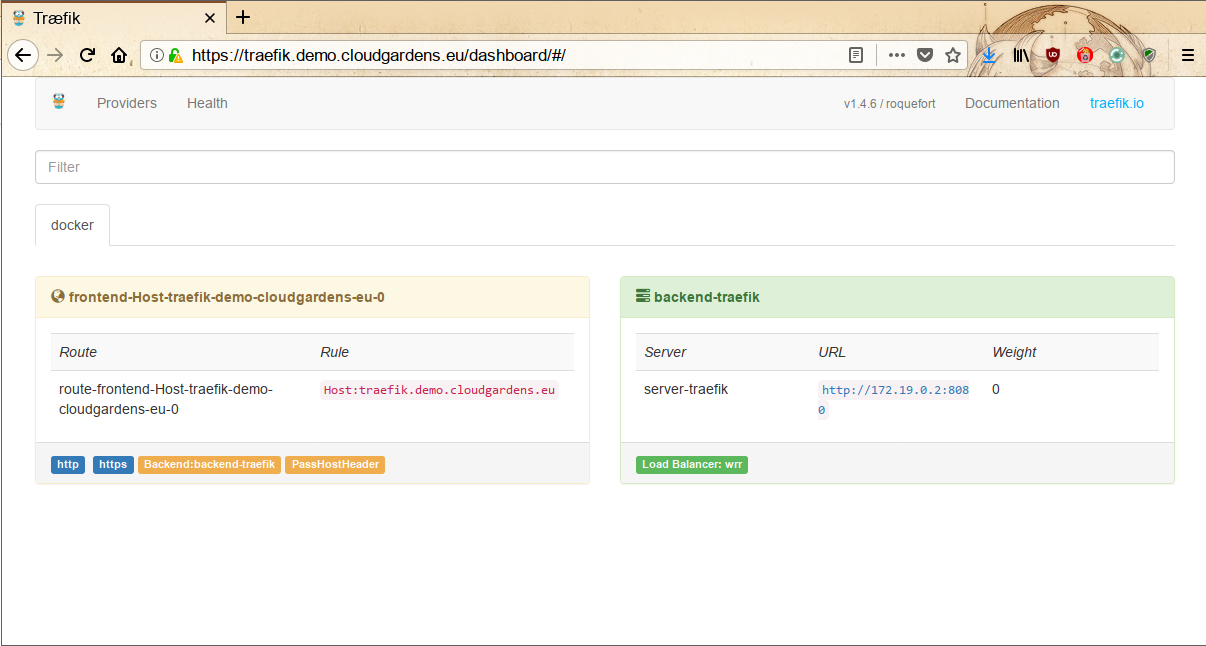
We know - there is no much information yet, but leave this window open. You have your træfik proxy up and running, waiting for more containers to come. You will see those containers on dashboard in few minutes.
We will use some popular web applications - wordpress and adminer. Both apps requires database, so let’s spin it up: docker run -d -e MYSQL_ROOT_PASSWORD="Test1234!" -l traefik.enable=false --name mariadb mariadb.
First app - adminer: docker run -d -l traefik.backend=adminer -l traefik.frontend.rule=Host:adminer.domain.tld -l traefik.docker.network=proxy -l traefik.port=8080 --network proxy --name adminer adminer
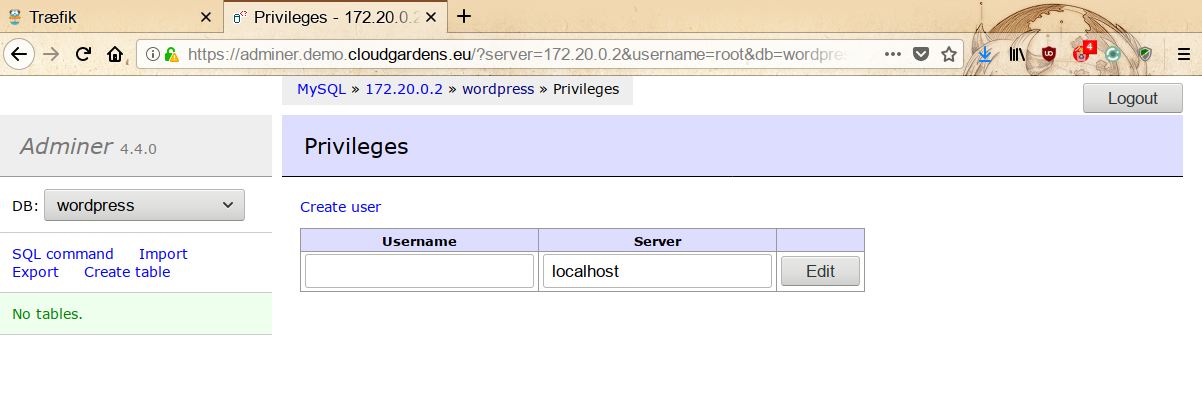
Go to https://adminer.domain.tld (Username: root, Password: what you set earlier) and add database for wordpress. Do not forget to create an user!
Perfect. Let’s spin up second app - wordpress. Get the database credentials from previous step. docker run -d -e WORDPRESS_DB_PASSWORD="wordpress-db" -e WORDPRESS_DB_USER="wordpress-user" -l traefik.backend=blog -l traefik.frontend.rule=Host:blog.domain.tld -l traefik.port=80 --network proxy --name blog wordpress. Wordpress oficial image listen on TCP\80, that’s why we put label traefik.port=80.
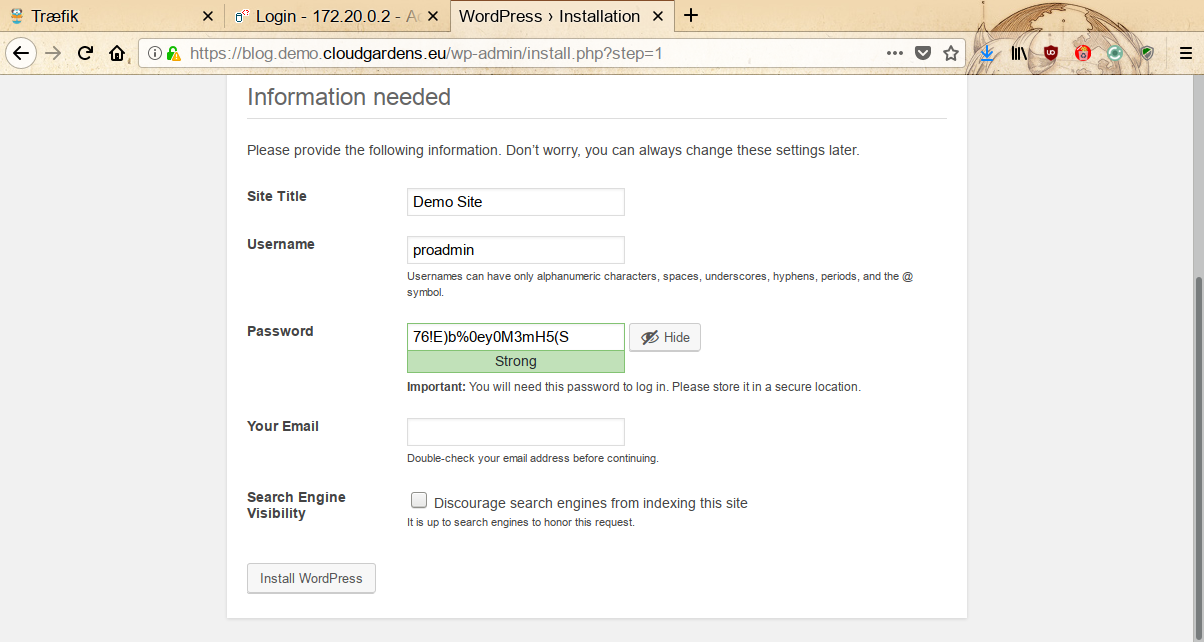
You can access your blog at https://blog.domain.tld. Just go through the installation guide and enjoy nice work.
Both sites are working. Go back to træfik’s dashboard and see how it changed.
You can also watch some videos if you want:

Warning
Due to TLS-SNI-01 challenge being temporary disabled by LE you should consider DNS Challenge instead: https://github.com/containous/traefik/issues/2691
Any questions about docker? Feel free to email us: contact@cloudgardens.eu