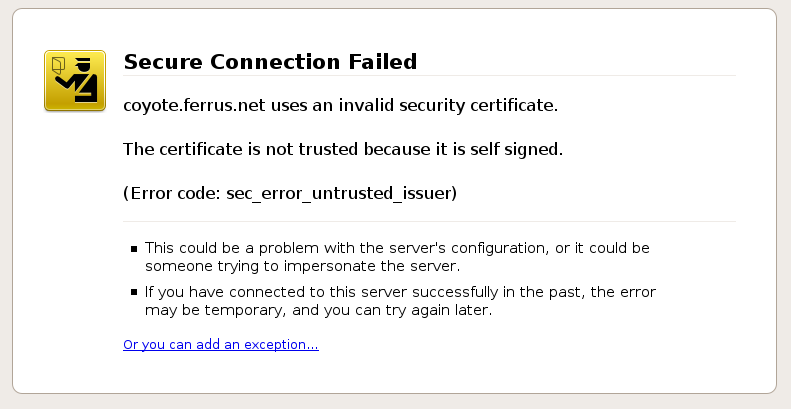
TLS connections (Transport Layer Security), which ensure integrity of data transmission and confidentiality, are used nowadays in many web applications. During connection establishment process the web browser, among other things, verifies if SSL certificate that was sent by server was issued by the trusted CA (Certification Authority). If so, web browser continues to download web page content. If not, it interrupts and asks user to make a decision.
In the past it happen few times, that the trusted CA issued wrong certificates, that were used by attackers to carry out man-on-the-middle attacks and to steal private user data.
At the beginning Public Key Pinning has been implemented by hardcoding certificates into web browsers. Only few domains were protected (big players like FB, Google, Twitter). Are You big enough?
HTTP Public Key Pinning is a powerful standard, that allows a host (web server) to instruct a browser to accept only defined (in HTTP header) public keys for a given period of time. Example header:
Public-Key-Pins:
pin-sha256="8RoC2kEF47SCVwX8Er+UBJ44pDfDZY6Ku5mm9bSXT3o=";
pin-sha256="78j8kS82YGC1jbX4Qeavl9ps+ZCzb132wCvAY7AxTMw=";
pin-sha256="GQGOWh/khWzFKzDO9wUVtRkHO7BJjPfzd0UVDhF+LxM=";
max-age=31536000; includeSubDomains
You can find more info about HTTP Public Key Pinning here: https://tools.ietf.org/html/rfc7469
What can go wrong?
Update expired certificates
It happened (https://www.smashingmagazine.com/be-afraid-of-public-key-pinning/) to Smashing Magazine site. They created new wildcard certificate, added it to PKP header, but the old header has told visitors that their browser should never accept any certificate that was not listed in the old PKP headers for the next 365 days.
Even worse, they could not roll back to old certificate since it had expired.
Server breach
Another scenario. If attacker gain access to web server / proxy server in front of app server or domain itself he can enable HPKP on your behalf. Visitors type your website address, go to your website and then browser get malicious HPKP configuration set by attackers. Eventually you get back access to your domain / web server and restore the content / configuration of your site, but none of the visitors will connect because of HTTP PKP policy picked up earlier. This is an example how security feature can be used by attackers to do harm.
Please be careful when deploying new security features. You need to know what you want to achieve and be careful about it. Feel free to contact us if you need assistance.