Hardening - (in computing) the process of securing a system by reducing its surface of vulnerability.
You may need to check many components, features and configuration files in order to safeguard your system from attack. There are some tools available around, made to make your live easier. OpenVAS, Lynis, and MBSA (for Microsoft users) just to name a few. In this blog post I will present how you can identify security concerns on UNIX-based operating systems using Lynis. Keep in mind that default baselines provided with scanners may not be sufficient to detect all incorrectly configured services on the target machine.
Background information
- Open Source Tool, Free to use
- Well-known and mature
- The best open source networking and security software 2016
- Packages available
- Widely used
Installation
Many distributions have the free Lynis version available in their repositories. You can also clone or download project files from GitHub (no compilation required):
# git clone https://github.com/CISOfy/lynis
# cd lynis
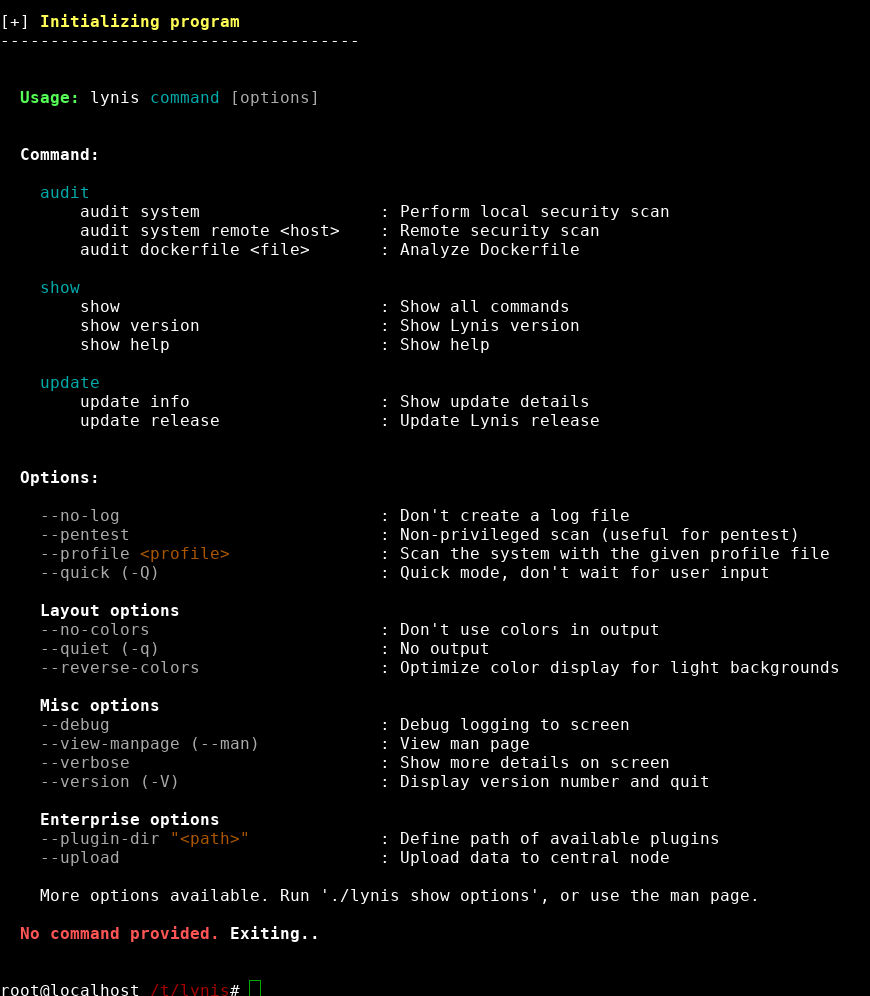
# ./lynis
Example of output:
If you have installed Lynis some time ago - check for update:
# ./lynis update info
Example of output:
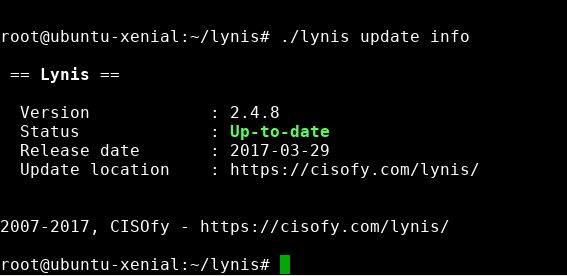
Now Lynis should be ready at your command.
Audit
To perform system audit, using the default profile provided by vendor of Lynis, execute below command:
# ./lynis audit system
And here is result of such an audit for a default Ubuntu Xenial (16.04.2 LTS) image I got from Atlas at the time of writing:
- Password policies:
Install a PAM module for password strength testing like pam_cracklib or pam_passwdqc [AUTH-9262] https://cisofy.com/controls/AUTH-9262/
Configure minimum password age in /etc/login.defs [AUTH-9286] https://cisofy.com/controls/AUTH-9286/
Configure maximum password age in /etc/login.defs [AUTH-9286] https://cisofy.com/controls/AUTH-9286/
- Package manager related stuff:
Install debsums utility for the verification of packages with known good database. [PKGS-7370] https://cisofy.com/controls/PKGS-7370/
Install package apt-show-versions for patch management purposes [PKGS-7394] https://cisofy.com/controls/PKGS-7394/
- Firewall not being configured:
- Configure a firewall/packet filter to filter incoming and outgoing traffic [FIRE-4590] https://cisofy.com/controls/FIRE-4590/
- Tips for openssh daemon:
Consider hardening SSH configuration [SSH-7408]
- Details : AllowTcpForwarding (YES –> NO) https://cisofy.com/controls/SSH-7408/
Consider hardening SSH configuration [SSH-7408]
- Details : ClientAliveCountMax (3 –> 2) https://cisofy.com/controls/SSH-7408/
Consider hardening SSH configuration [SSH-7408]
- Details : Compression (DELAYED –> NO) https://cisofy.com/controls/SSH-7408/
Consider hardening SSH configuration [SSH-7408]
- Details : LogLevel (INFO –> VERBOSE) https://cisofy.com/controls/SSH-7408/
Consider hardening SSH configuration [SSH-7408]
- Details : MaxAuthTries (6 –> 2) https://cisofy.com/controls/SSH-7408/
Consider hardening SSH configuration [SSH-7408]
- Details : MaxSessions (10 –> 2) https://cisofy.com/controls/SSH-7408/
Consider hardening SSH configuration [SSH-7408]
- Details : PermitRootLogin (WITHOUT-PASSWORD –> NO) https://cisofy.com/controls/SSH-7408/
Consider hardening SSH configuration [SSH-7408]
- Details : Port (22 –> ) https://cisofy.com/controls/SSH-7408/
Consider hardening SSH configuration [SSH-7408]
- Details : TCPKeepAlive (YES –> NO) https://cisofy.com/controls/SSH-7408/
Consider hardening SSH configuration [SSH-7408]
- Details : UsePrivilegeSeparation (YES –> SANDBOX) https://cisofy.com/controls/SSH-7408/
Consider hardening SSH configuration [SSH-7408]
- Details : X11Forwarding (YES –> NO) https://cisofy.com/controls/SSH-7408/
Consider hardening SSH configuration [SSH-7408]
- Details : AllowAgentForwarding (YES –> NO) https://cisofy.com/controls/SSH-7408/
As you see, suggestions include links to knowledge base provided by the vendor.
The results show that in case of default installation of Ubuntu 16.04.2 LTS there is a clearly a huge margin for improvement. But do not be suprised - from my experience there is no such thing like default installation of Linux/UNIX distribution being fully secured.
All details are also stored in a log file. Findings and other discovered data are stored in a report file. This can be used to compare difference between audits. Lynis can run as a cronjob (use --cron option to perform scan with cron safe options - no colors, no questions, no breaks).
Customization
Want to create your own tests? Have a look at Lynis SDK.
30 seconds demo
Everybody loves to read blog posts, right? If not - here is 30 seconds demo made by CISOfy.